Tag: CYBERSECURITY
The human will to innovate is seemingly relentless. The history of our species is one of continual development, with the last 350 years, in...
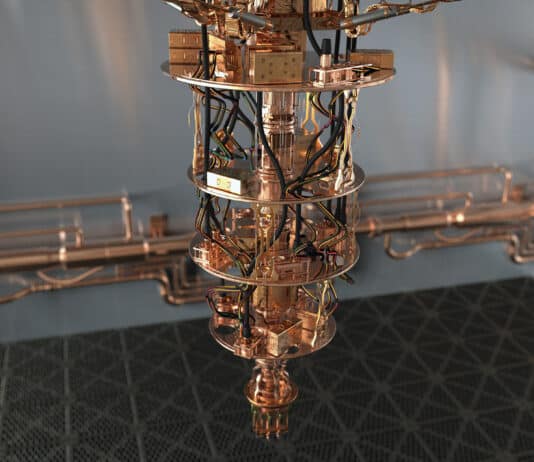
The secret sauce of quantum computing, which even Einstein called "spooky," is the ability to generate and manipulate quantum bits of data or qubits. Certain computational tasks can be executed exponentially faster on a quantum processor using qubits, than on a classical computer with 1s and 0s. A qubit can attain a third state of superimposition of 1s and 0s simultaneously, encode data into quantum mechanical properties by "entangling" pairs of qubits, manipulate that data and perform huge complex calculations very quickly.
When microwave ovens first arrived on the market in 1967 they were met with public skepticism. Perhaps it was because, not long before, the...
The timeline of human history is marked by inflection points of major technological advancement. The plow, the printing press, the telegraph, the steam engine,...
Canada has been investing in machine learning and artificial intelligence (AI) for longer than most of the industrialized world. Dr. Geoff Hinton of Google...
NFC is a short range two-way wireless communication technology that enables simple and secure communication between electronic devices embedded with NFC microchip. NFC technology...
Radio-Frequency Identification (RFID) is a technology commonly used for identification, status administration and management of different objects. It is important for people identification, as it...
If you've ever been to an expensive restaurant and ordered a familiar dish like, say, lasagna, but received a plate with five different elements...
The Wi-Fi represents wireless technology that includes the IEEE 802.11 family of standards (IEEE 802.11a, IEEE 802.11b, IEEE 802.11g, IEEE 802.11n, IEEE 802.11ac, etc.)....
Bluetooth is short-range wireless communications technology based on the IEEE 802.15.1 protocol. It works in a crowded license free 2.4 GHz frequency band and...
Zigbee technology introduction
Zigbee is wireless PAN (Personal Area Network) technology developed to support automation, machine-to-machine communication, remote control and monitoring of IoT devices. It...
I get accused of focusing too much on 5G as the only future IoT connectivity option. I do write a lot about how 5G...
Because it demands so much manpower, cybersecurity has already benefited from AI and automation to improve threat prevention, detection and response. Preventing spam and identifying malware are already common examples. However, AI is also being used – and will be used more and more – by cybercriminals to circumvent cyberdefenses and bypass security algorithms. AI-driven cyberattacks have the potential to be faster, wider spread and less costly to implement. They can be scaled up in ways that have not been possible in even the most well-coordinated hacking campaigns. These attacks evolve in real time, achieving high impact rates.
In 2013, George F. Young and colleagues completed a fascinating study into the science behind starling murmurations. These breathtaking displays of thousands – sometimes...
Not even 30 years separate us from the end of the Cold War. Yet, we appear to be witnessing the emergence of a new...